- The Blockchain for Africa
- info@horizonafrica.io
Blockchain in Mauritius – World Blockchain STO Summit

The World Blockchain STO Summit was held in Mauritius on the 31st July 2019 at the Caudan Arts Centre. It regrouped people with expertise from different sectors to share their opinions about Security Tokens and Security Tokens Offering (STOs) in Mauritius and around the world. Suyash Sumaroo, one of Horizon Africa’s Co-Founders, gave a talk about STOs and smart contracts, and the technical implications of a security token.
Suyash has also been among the first companies in Mauritius to launch a commercial blockchain-based application in the form of a document management system (StoragePlus.io) which allows for document integrity and authenticity via smart contracts. He started studying STOs and their implementation sometime back when he, along with Akash (Co-Founder of Horizon Africa) were working on a project in a technical advisory role for a Mauritian management company. Suyash is still very active in the Blockchain sector in Mauritius.
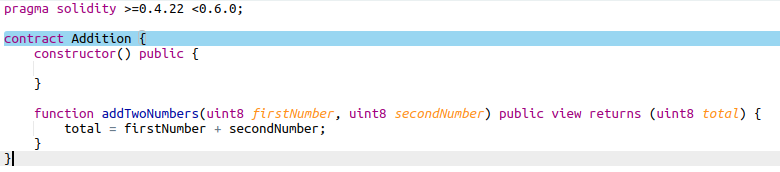
It may seem daunting at first, and gibberish to a lot of people. However, this piece of smart contract does one simple thing: it just adds 2 numbers and gives you the total. The point to remember is that a smart contract is like anything else that already exists in terms of software. It can be as complex or as simplex is needed. Smart contracts are not really that smart. They are simply instructions that are given to a blockchain to follow rules.
On-chain governance allows the setting up of rules to manage a token directly in the blockchain. Conditions are defined in a smart contract and the blockchain will take these instructions, convert them to rules and make sure that these rules are followed.
Off-chain governance, on the other hand, implies the use of centralized processes to set up rules which need to be followed.
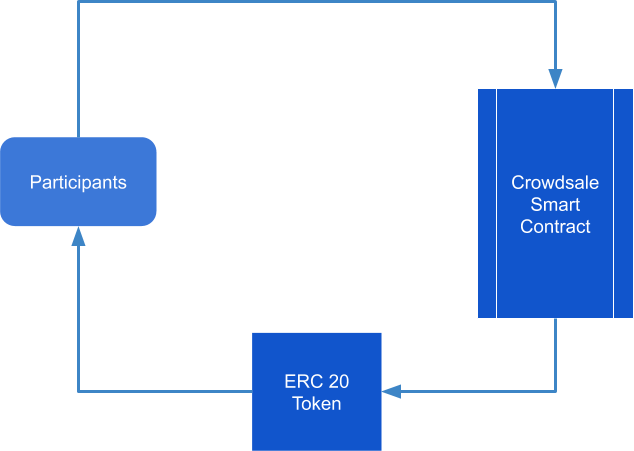
The interactions are relatively simple in that the participants interact with the crowdsale smart contract, by sending cryptocurrencies and in return, getting digital assets. The following diagram perfectly illustrates the interactions and components of an ICO.
A STO, on the other hand, require the need for on-chain transactions along with off-chain governance. In this system, more parties are involved:
The standard is actually a set of other standards which define the different components required in a STO.
ERC 1594 defines rules which allow the transfer of security tokens from one party to another, managing things like whether a party has gone through the right kyc process and other regulatory requirements. Just to compare, if you want to do a transfer in the ERC 20 smart contract, in a traditional ICO, the only requirement is that you have is enough balance.
Securities are often associated with documents that can come from different sources but which are needed from a regulatory perspective to make any security token transaction possible and valid.
ERC 1644 which is about controller operations - The ownership of a security token is not entirely determined by the blockchain or whoever holds the private keys. Instead, regulators or parties with the required permissions should have the required authority and technical ability to perform actions like reversing transactions, forcing transfers, and any other actions which they are legally entitled to perform.
Background of Suyash Sumaroo
Suyash has been in the blockchain space for the past 3 years and has been working in different projects ranging from ICOs to cryptocurrency exchanges. More recently, Suyash has been involved in CryptoFish, which is a platform that facilitates the purchase of CryptoCurrencies worldwide through their online and mobile interface specifically designed to take the complexity out of the process.Suyash has also been among the first companies in Mauritius to launch a commercial blockchain-based application in the form of a document management system (StoragePlus.io) which allows for document integrity and authenticity via smart contracts. He started studying STOs and their implementation sometime back when he, along with Akash (Co-Founder of Horizon Africa) were working on a project in a technical advisory role for a Mauritian management company. Suyash is still very active in the Blockchain sector in Mauritius.
What are Smart Contracts?
The most obvious question to start with is the following question: what is a smart contract? A lot of people have probably heard about smart contracts and think that it is something extremely complex. This cannot be further from the truth. The following is an example of a smart contract.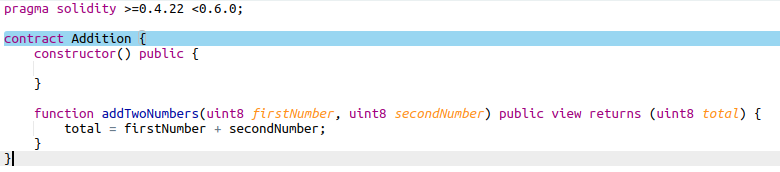
It may seem daunting at first, and gibberish to a lot of people. However, this piece of smart contract does one simple thing: it just adds 2 numbers and gives you the total. The point to remember is that a smart contract is like anything else that already exists in terms of software. It can be as complex or as simplex is needed. Smart contracts are not really that smart. They are simply instructions that are given to a blockchain to follow rules.
On-Chain and Off-Chain Governance
Besides smart contracts, another very important concept when we are talking about security tokens is about on-chain and off-chain governance. This sits at the core of how a security token is created and managed.On-chain governance allows the setting up of rules to manage a token directly in the blockchain. Conditions are defined in a smart contract and the blockchain will take these instructions, convert them to rules and make sure that these rules are followed.
Off-chain governance, on the other hand, implies the use of centralized processes to set up rules which need to be followed.
Differences between ICOs and STOs
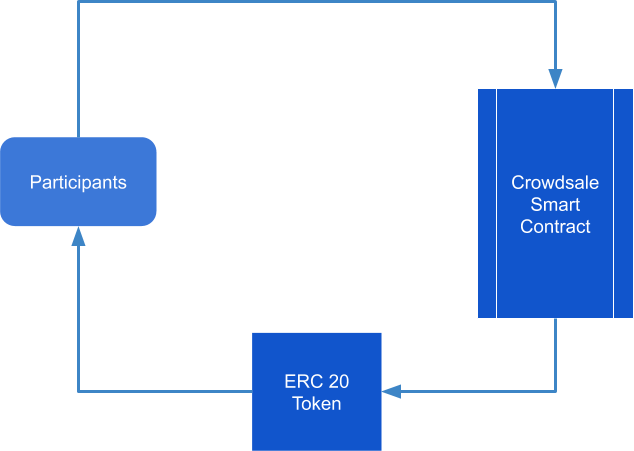
In an ICO (Initial Coin Offering), three different parties are involved including:- The participants, that is, people or companies who are willing to buy tokens with cryptocurrencies.
- The Crowdsale smart contract - a smart contract which manages interactions between participants and the ICO.
- The digital asset, which is normally represented by an ERC 20 token.
The interactions are relatively simple in that the participants interact with the crowdsale smart contract, by sending cryptocurrencies and in return, getting digital assets. The following diagram perfectly illustrates the interactions and components of an ICO.
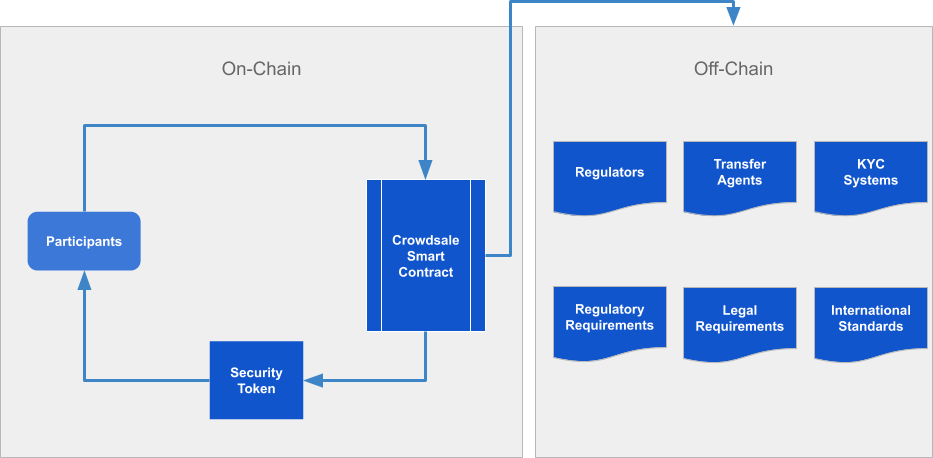
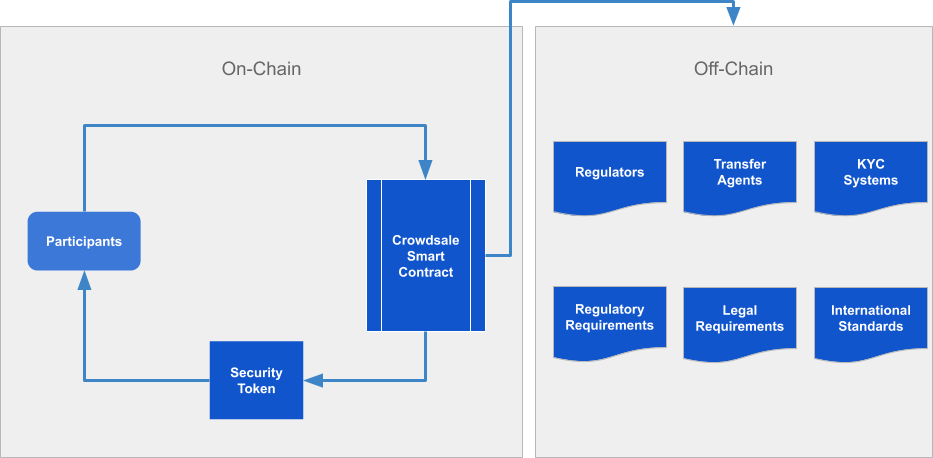
A STO, on the other hand, require the need for on-chain transactions along with off-chain governance. In this system, more parties are involved:
- Participants are still involved.
- Crowdsale smart contract are still present.
- Instead of 'normal' tokens, security tokens are issued and distributed.
- Regulators
- Third-party transfer agents
- KYC Systems
- Any other entity which is required by the legal jurisdiction and regulations
Implementation considerations
Currently, there are different ways that a STO can be conducted. This is a list of standards which exist and which cover nearly all aspects of conducting a STO:- ERC - 1400/1411
- ERC - 1462
- ERC - 1600
- ST - 20
ERC 1400/1411
The ERC 1400 is backward compatible with the ERC 20 standard which is still hugely popular and which is supported by most systems including wallets and crypto exchanges.The standard is actually a set of other standards which define the different components required in a STO.
- ERC-1410: Fungible / Vesting / Time Locks / Voting
- ERC-1594: Token Transfer Rules / KYC / Regulatory
- ERC-1643: Document Management
- ERC-1644: Controller Operations
ERC 1594 defines rules which allow the transfer of security tokens from one party to another, managing things like whether a party has gone through the right kyc process and other regulatory requirements. Just to compare, if you want to do a transfer in the ERC 20 smart contract, in a traditional ICO, the only requirement is that you have is enough balance.
Securities are often associated with documents that can come from different sources but which are needed from a regulatory perspective to make any security token transaction possible and valid.
ERC 1644 which is about controller operations - The ownership of a security token is not entirely determined by the blockchain or whoever holds the private keys. Instead, regulators or parties with the required permissions should have the required authority and technical ability to perform actions like reversing transactions, forcing transfers, and any other actions which they are legally entitled to perform.